Token Presale Platform Turnkey Solution
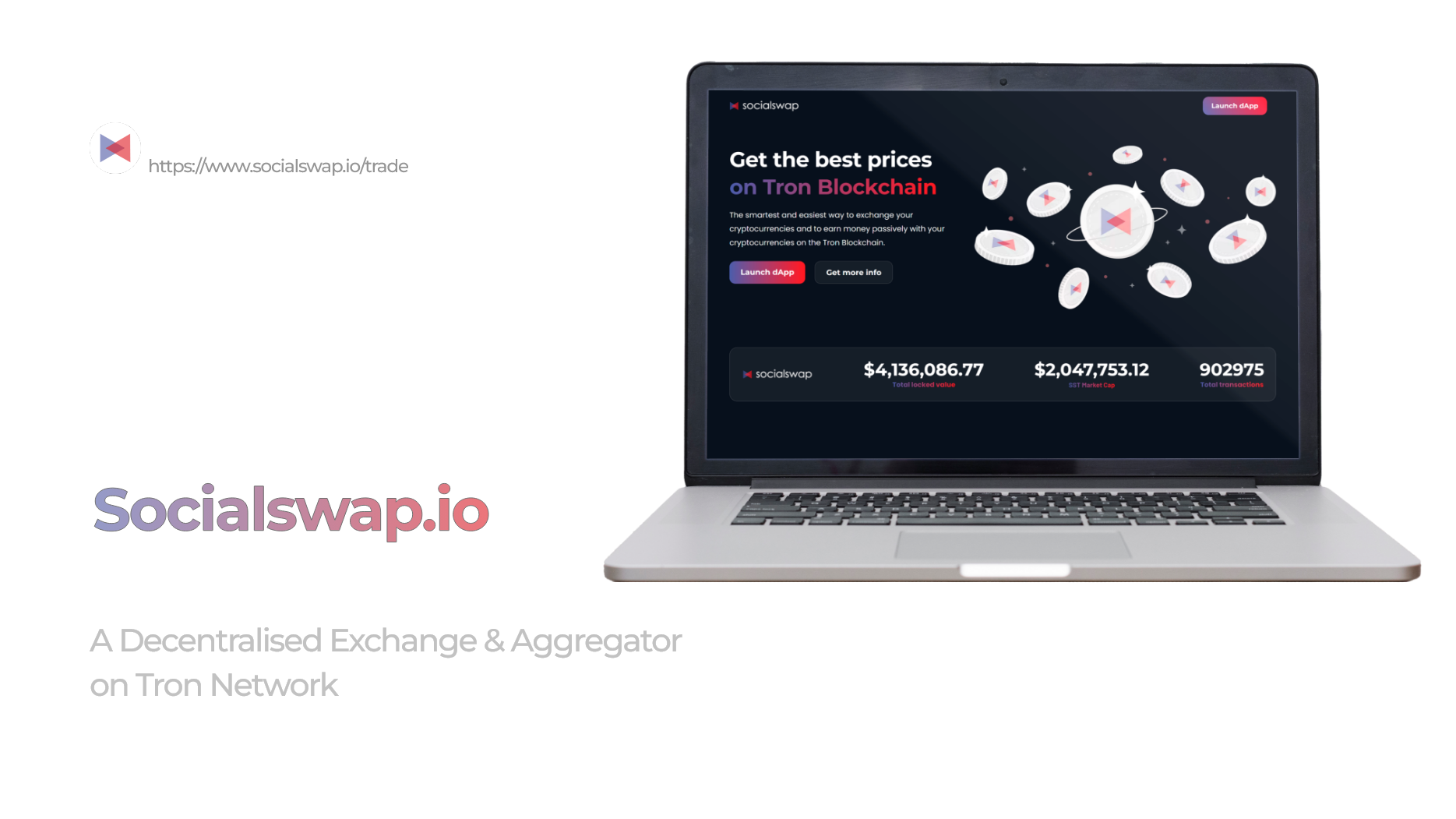
Welcome to the next generation of presale management with our Token Presale Platform Turnkey Solution. Harness the power of popular blockchain networks like Ethereum, Tron, Polygon, Binance Smart Chain (BSC), Polkadot, Bitcoin, Litecoin, and Dogecoin, all in one production ready solution.
What is an ICOs?
An ICO, or Initial Coin Offering, is a popular way of crowdfunding in the blockchain space. In an ICO, startups offer tokens in exchange for cryptocurrency from investors. Tokens serve as the internal currency for the project and often provide access to certain platform features. However, ICOs are not regulated and lack investor protection, anonymity, and an MVP. They are similar to crowdfunding campaigns, but lack the legal boundaries and other safeguards. To start an ICO, a company only needs a website and a wallet address to receive funds.
Liquidity:
This allows investors to quickly buy or sell tokens and receive their return on investment in a timely manner. The secondary market provides more stability and security for investors, which can increase overall trust in the project and attract more investment. By having a secondary market for tokens, companies can receive more funding and investors can see a quicker return on their investment.
Decentralization:
Additionally, participating in ICOs can be done from anywhere in the world, as long as there is access to the internet and the necessary funds to participate. However, it's important to note that ICOs are highly speculative investments and there are risks involved, such as fraud, hacking, or the failure of the project to deliver on its promises. As with any investment, it's crucial to do thorough research and consult with a financial advisor before participating in an ICO.
Transparency:
ICOs, on the other hand, offer the opportunity for anyone to invest, regardless of their relationship with the founder or company. They are open to the public and accessible at any time, providing a level playing field for all investors.
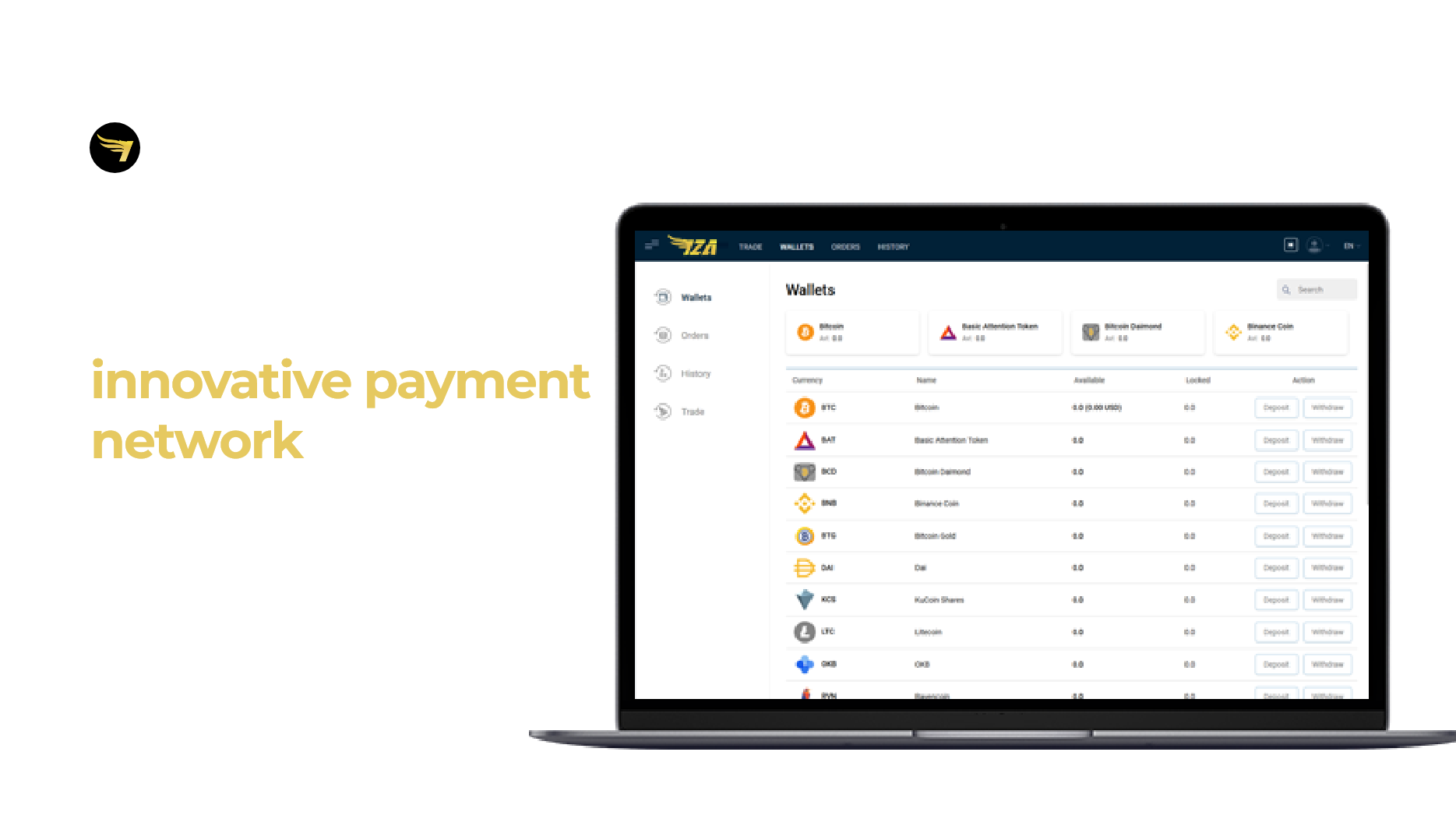
What is an IEO?
IEOs (Initial Exchange Offerings) share similarities with ICOs (Initial Coin Offerings), but they are conducted through a trading platform, which takes responsibility for managing the smart contract, conducting KYC (Know Your Customer) checks, marketing, and providing the token with immediate secondary market availability after the initial issuance. IEOs are often held on exchange platforms and issuers have to pay a listing fee and a portion of the tokens sold during the IEO. IEOs provide a higher level of credibility and reliability compared to ICOs.
The Exchange Platform Provides the Following Support:
IEO (Initial Exchange Offering) and STO (Security Token Offering) are two different forms of crowdfunding in the blockchain space. IEOs are conducted entirely on a cryptocurrency exchange platform, while STOs represent a security token that represents ownership in an underlying asset, such as a company or real estate.
IEOs offer a win-win situation for both businesses and exchange platforms. The exchange provides support in listing, marketing, smart contracts, and other aspects of the project, which reduces the cost for businesses in their fundraising campaign. The exchange also benefits from its existing user base and fees generated from the IEO. Investors can participate in the IEO by creating an account on the exchange platform and purchasing tokens. Both businesses and exchange platforms can benefit from this arrangement.
ROI: A Significant Return on Investment
In summary, businesses choosing an IEO as their fundraising strategy have the potential to benefit from the support of the exchange platform, reduced fundraising costs, increased credibility, and access to the platform's existing user base. Exchanges benefit from the partnership through fees, token fees, and marketing collaborations. However, it should also be noted that businesses will have to initially invest a large sum of money.
Integrity and Trust:
Yes, that's correct. A project's listing on a reputable exchange can greatly increase its credibility and can also make it easier for investors to trade the tokens. However, it's important for both the exchange and the project to thoroughly vet each other and ensure that there is alignment on the project's goals and execution plans. If a project fails to deliver on its promises, it can harm the reputation of both the project and the exchange.
What is an STO?
STOs are generally considered a more secure form of fundraising compared to ICOs because they follow stricter regulatory requirements, such as KYC and AML, and their tokens are considered securities. STOs offer a higher level of transparency and security, but also come with increased administrative costs and regulatory compliance requirements, which can make them more challenging for startups to undertake. Despite the added hurdles, many startups are turning to STOs as a way to raise capital in a secure and transparent manner.
Costs are Lower than IPOs:
Yes, that's correct. STOs offer a more cost-effective alternative to traditional initial public offerings (IPOs) as they eliminate intermediaries and reduce the cost of compliance with regulatory requirements. Additionally, STOs can potentially increase investment opportunities for investors as more startups are able to raise capital in this manner. However, it's important to keep in mind that STOs are still subject to regulation and compliance requirements, and companies must follow these rules in order to issue security tokens.
Flexibility:
Going public through traditional methods can also be time-consuming and involves a lot of paperwork. STOs offer a faster and more efficient way for businesses to raise capital, allowing them to concentrate on their goals and mission without being bogged down by the listing process. Additionally, STOs are not limited to a specific exchange, offering greater flexibility for businesses to trade on multiple platforms. However, it is important to keep in mind that STOs still must comply with securities regulations, which may impose restrictions on their operations.
Accessibility Around the World:
However, the regulatory framework for security tokens varies from country to country, which can impact their ease of trade. In addition, security tokens are subject to various laws and regulations, including those related to anti-money laundering (AML) and know-your-customer (KYC) requirements, which can add complexity to the buying and selling process. It is important for investors to thoroughly understand the legal and regulatory framework of the country where they plan to invest in security tokens.
Token Presale Platform Turnkey Solution Key Features
Token Presale Platform Turnkey Solution is an all-in-one package designed to simplify and streamline the token presale process, from creation to conclusion, while providing the necessary tools, security measures, and support to ensure success. It is suitable for various types of users, from startups to established companies, looking to conduct a token presale on multiple blockchain networks.

Multi-Chain Support
Enables token presales across various blockchain networks, including Ethereum, Tron, Polygon, BSC, Polkadot, Bitcoin, Litecoin, and Dogecoin, providing versatility and broad accessibility.

User-Friendly Interface
Features an intuitive design that simplifies the creation, launch, and management of token presales, catering to both novices and experts.
High Security Standards
Incorporates robust security protocols to safeguard transactions and user information, aligning with industry best practices.

Scalable & Customizable
Offers flexibility in hosting different types and sizes of presales, with the ability to tailor the platform to specific project requirements.
Comprehensive Analytics
Provides detailed insights and real-time statistics to track and analyze the presale's performance, supporting informed decision-making.

Automated Token Distribution
Includes built-in automation for efficient token distribution to participants after the presale, based on pre-set rules and allocations.
Regulatory Compliance
Ensures adherence to legal and regulatory standards across various jurisdictions, mitigating legal risks.

Vesting Feature
Offers a vesting schedule for tokens, allowing for controlled and gradual release of tokens to participants, enhancing trust and stability.
Payment Methods
Supports both fiat and crypto payment methods, enabling a broader range of participants to easily invest in the presale, thereby fostering inclusivity and convenience.
How the Token Presale Platform Works?
The Token Presale Platform Turnkey Solution simplifies and streamlines the entire presale process, from creation to conclusion, by offering all the essential tools and features in one comprehensive package. It's designed to meet the needs of various projects, ensuring a successful and efficient token presale.
01
Create Your Presale:
Select Blockchain Network: Choose from the supported networks like Ethereum, Tron, Polygon, BSC, etc.
Define Token Parameters: Set the token name, symbol, total supply, and other essential details.
Set Presale Terms: Determine the start and end dates, pricing, caps, and any specific rules or conditions. Customize Your Settings:
02
Customize Your Settings:
Set Vesting Schedule: If desired, create a vesting schedule for a gradual release of tokens to participants. Design User Interface: Customize the look and feel of the presale page to align with your brand.
Design User Interface: Customize the look and feel of the presale page to align with your brand.
Configure Payment Methods: Enable both fiat and crypto payment methods, and select supported currencies. Launch & Monitor:
03
Launch & Monitor:
Launch Presale: Make the presale live and share the link with potential participants.
Monitor Performance: Utilize comprehensive analytics to track participant behavior, funds raised, token allocation, etc.
Engage Participants: Send updates, announcements, or support through various communication channels.
04
Finalize & Distribute:
Close Presale: Once the presale period ends or the cap is reached, close the presale.
Verify Compliance: Ensure all transactions comply with predefined rules and regulatory requirements.
Distribute Tokens: Use the automated token distribution feature to send tokens to participants according to their contribution and any applicable vesting schedules.
Provide Support: Continue to offer support to participants regarding any queries or issues related to token distribution, vesting, etc.
05
Payment Processing:
Accept Payments: Participants can contribute using their preferred payment method, whether fiat or crypto.
Secure Transactions: All transactions are secured using high security standards, with funds held safely until distribution.
Provide Receipts: Generate and send payment receipts to participants for their records.

06
Regulatory Oversight:
Maintain Compliance: Regularly check for adherence to legal and regulatory standards to mitigate legal risks.
Report as Needed: Generate and submit any required reporting to regulatory bodies.

07
Post-Presale Activities:
Review Performance: Participants can contribute using their preferred payment method, whether fiat or crypto.
Communicate with Participants: All Keep participants informed about project developments, future token releases, or other relevant news.
Plan Next Steps: Depending on the project's roadmap, plan and execute subsequent phases, whether further token sales, product development, marketing, etc.
Data Security
Backup of data in two modes
Two data backup modes are available: real-time replication and daily scheduled backup. Real-time replication instantly mirrors changes, providing continuous protection. On the other hand, the daily scheduled backup saves modified data at predetermined intervals, ensuring regular data preservation. Choose the mode that suits your needs best.
Authorization through
two-factor authentication
Exchange employs two-factor authentication to bolster the security of multiple admin panels. This process entails sending a secure link via email and requesting a token, providing an extra layer of protection against unauthorized access to the system. By requiring both the secure link and token, the system ensures enhanced authorization measures, safeguarding sensitive information and bolstering overall security.
IP-based access restrictions
IP-based access restrictions involve associating an IP address with a login password or key to control system access. In Exchange, for instance, the payment system can only be accessed from a pre-defined IP address, ensuring secure and limited access to authorized users. This mechanism adds an extra layer of protection, mitigating potential unauthorized access and enhancing overall security measures.
Database with encryption
Client personal information is stored in an encrypted database partition, ensuring that the data remains inaccessible even from the server itself. This encryption measure provides an additional layer of security, safeguarding sensitive information from unauthorized access and protecting the privacy of clients' data.
Replication of databases securely
Secure replication of databases is achieved through SSL-enabled database replication, effectively eliminating the risk of man-in-the-middle (MITM) attacks. By employing SSL encryption, the data transmission between the databases is protected from interception and unauthorized access, ensuring the integrity and confidentiality of the replicated data.
Access Security
Access logs
For auditing and security purposes, all database server accesses are logged, providing a comprehensive trail of actions, including details like timestamps, users, operations performed, and data involved. This meticulous logging ensures accountability, helps detect potential breaches, and ensures compliance with regulatory requirements and data governance practices.
External data exchange that is secure
To ensure secure external data exchange, a unique authentication key is used when interacting with external systems like payment systems. After each data exchange, the signature is verified to guarantee its authenticity and maintain a high level of data security and integrity throughout the process. This approach provides a robust and reliable method to safeguard sensitive information during external data transactions.
SSH Keys
SSH keys are employed by Ment Tech personnel for server access, with access limited to a select few individuals who use encrypted disks on their computers. This measure effectively mitigates data breach risks resulting from laptop theft, ensuring the utmost confidentiality of sensitive information. By combining SSH keys and encrypted disks, the company ensures robust security measures are in place to safeguard critical data from unauthorized access.
Document security
Document security is prioritized by not storing any client documents within our database. Instead, data processing takes place through a cloud-based solution offered by a third-party provider. For utmost protection, all client documents are securely stored by third-party KYC (Know Your Customer) providers, strictly adhering to the contract terms. This approach ensures the confidentiality and integrity of sensitive client information.
Change monitoring
Change monitoring is a crucial aspect of our security measures. We conduct continuous monitoring of critical data, including password hashes. In case of any alterations, immediate notifications are sent through two separate channels, ensuring real-time awareness and bolstering our security protocols. This proactive approach helps safeguard against potential security breaches and enhances overall data protection.
High-level DDoS mitigation is employed to secure our servers, preventing disruptive bad traffic while allowing good traffic to pass through smoothly, ensuring high availability and optimal performance of websites, applications, and APIs.
Dedicated Support Team
We are dedicated to providing support and taking responsibility when you need assistance, and will never pass the buck by saying it's not our issue. We maintain a comprehensive logging system for all comments and details from our developers across our entire product line, ensuring that we are able to assist you effectively without having to repeatedly ask for information.
Resources & Tutorials
Ment Tech places a strong emphasis on delivering exceptional user experience. This is achieved by partnering closely with clients and providing a wealth of tutorials and resources to assist with technical needs. The team is knowledgeable and dedicated to ensuring a seamless experience.
Instruction
At Ment Tech, education is a key part of our service offering. We strive to provide our clients with the knowledge and understanding they need to succeed, which is why we offer video training and demonstrations in addition to a wide range of tutorials and materials. Our goal is to ensure the ultimate user experience for our clients.
Dedicated Experts for Each Project
At Ment Tech, we take great pride in our commitment to excellence. With an unwavering dedication to delivering successful outcomes, we ensure that every project is handled by a team of dedicated experts. These professionals are carefully assigned based on their specialized skills and knowledge, ensuring that each endeavor receives the attention it deserves. Our emphasis on English language proficiency further ensures effective communication and understanding throughout the entire project lifecycle. Experience the difference of having expertly assigned teams working passionately to achieve your goals .
Project Manager
We provide each of our clients with a dedicated project manager, readily available to address inquiries and cater to their specific needs.

QA Engineer
All our projects are supported by a dedicated QA Engineer, ensuring meticulous testing and quality assurance to meet the highest standards of excellence.
DevOps Engineer
Our dedicated DevOps Engineer ensures seamless integration, continuous delivery, and efficient infrastructure management for successful project development.
UI & UX Engineer
Our UI/UX Engineer crafts intuitive designs and seamless interactions, delivering exceptional user experiences for your project.

Blockchain Engineer
The Blockchain Full-Stack Engineer develops innovative solutions, combining front-end and back-end expertise for execution.
Business Analyst
Our Business Analyst plays a crucial role in analyzing and interpreting data to inform effective business strategies, ensuring successful project outcomes.
Some of Our Exceptional Achievements
Interested in Working Together? Let's Talk!
We're interested in hearing your ideas and discussing them further. Before we proceed, we will send you a Non-Disclosure Agreement (NDA) to ensure the confidentiality of all information shared. Your privacy is of utmost importance to us.
- 2019 - 2025 © Ment Tech Labs Pvt. Ltd